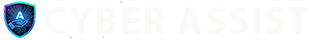
A Real Estate Agent’s Business Almost Vanished
The digital world often feels abstract, a series of clicks and screens. But for “Sarah,” a successful real estate agent with a thriving business in a competitive market, the digital world became terrifyingly, destructively real. Her story is a stark reminder that cyber threats aren’t just headlines; they’re direct assaults on livelihoods and reputations.
It started innocently enough, as most sophisticated attacks do. Sarah received an email, seemingly from a reputable title company she frequently worked with. It contained a link, purportedly to an updated closing document. In her fast-paced world, a quick click and download of what appeared to be a standard installer file was a routine action. What she didn’t know was that she had just opened the door to a nightmare.
That installer was not an update; it was a potent strain of remote access trojan (RAT), meticulously designed to bypass her basic, free antivirus software without so much as a blip. From that moment, an invisible intruder had unfettered access to her digital life. They could see her screen, access her files, read her emails, and, most critically, control her banking applications. Sarah went about her busy week, unaware that her computer was no longer truly hers.
Over the next five agonizing days, the hackers moved with chilling precision. They weren’t just looking for quick cash; they were conducting a surgical strike on her entire financial ecosystem. Using her computer, her identity, and her accounts, they initiated three separate wire transfers, meticulously spaced to avoid immediate suspicion. Each transfer siphoned off significant sums, culminating in a devastating total of almost $60,000 gone from her business accounts. The funds vanished into untraceable cryptocurrency wallets, the digital equivalent of disappearing without a trace.
But the financial hemorrhaging was only the beginning. The invaders didn’t stop there. With the same stealth, they meticulously infiltrated all of her linked financial accounts – personal savings, investment portfolios, and lines of credit. They didn’t necessarily empty them immediately; the intent seemed to be to map out her entire financial footprint, creating backdoors and vulnerabilities for future exploitation. It was an inventory of her wealth, a blueprint for total financial devastation.
The shocking discovery came when Sarah’s bank flagged an unusual transfer, far too late to stop the bulk of the damage. The subsequent investigation was a nightmare of its own. It took months of forensic analysis, IT specialists poring over every byte of data, and extensive coordination with financial institutions, to even begin to understand the depth of the attack. They discovered that the malware had been designed to mimic legitimate system processes, making it virtually invisible to standard detection methods. It had even installed keyloggers to capture new passwords she created in a desperate attempt to regain control.
The emotional and professional toll on Sarah was immense. Beyond the staggering financial loss, which took a significant chunk out of her working capital, there was the profound sense of violation and vulnerability. Her reputation, built over years of trusted service, felt fragile. The process of securing her systems involved a complete overhaul: wiping and rebuilding every device, implementing multi-factor authentication everywhere, and investing in advanced, managed endpoint security that actually monitors for suspicious behavior, not just known viruses.
Sarah’s story is a harrowing testament to the inadequacy of basic cybersecurity in today’s threat landscape. It’s a stark warning to every business professional: the cost of a “free” solution can be your entire livelihood. Are you truly protected, or are you just waiting for your own digital nightmare to begin?